This week's Firewall Fridays hit different. In episode 52 of the Code to Cloud podcast, cybersecurity advisor Dom Vogel and I sat down for a conversation that should be required listening for every business owner, CFO, and IT leader in Western Canada — and honestly, anywhere.
We covered two stories. The first involves a construction company that lost nearly $500,000 because someone said the words "state of the art" and nobody asked a follow-up question. The second involves a $300 TV box from a big-box retailer that turned out to be a sophisticated Chinese espionage device — with a microphone in the remote, SCADA exploit code baked in, and a direct pipeline back to a botnet responsible for the largest DDoS attack ever recorded. The original research came out of the U.S. oil and gas sector, but the implications hit close to home for anyone in Western Canada's energy industry.
You can't make this stuff up.
What's Inside
- How untested "state-of-the-art" backups cost one company $500K
- The organizational failure pattern that made it possible
- Why cloud-managed backups beat on-prem for 95% of Alberta businesses
- Full technical breakdown of the SuperBox espionage device
- How U.S. oil and gas workers were targeted — and why it matters for Western Canada
- The MLM distribution model and psychological manipulation behind it
- Detection indicators for IT security teams
- Complete investigation timeline and further reading
Listen to the Full Episode
Story One: The $500K Backup That Never Worked
Dom Vogel is one of the sharpest cybersecurity operators I know — years of incident response, security architecture, and advisory work across Western Canada. When he tells you a story, it's because he's lived it. This one started with a phone call.
Dom got a call from the CFO of a mid-sized construction company, in a panic. They were in the middle of a major project, needed to submit critical files to hit milestones, and couldn't access anything. The IT person had told everyone the backup architecture was "state of the art." Problem is — it had never been tested.
When Dom dug in, the reality was brutal. The IT person — who happened to be the brother-in-law of one of the executives — hadn't tested the backup system since before he last changed the architecture. The most recent recoverable data went back to October 2025. The critical files had been created months after that.
The company had three options — none of them good:
- Manually recreate every file from scratch
- Pay the ransom and hope the files come back intact
- Go to the client, admit the delay, and negotiate for more time
They chose option three — and it came with a $500,000 financial penalty from their client for delaying the project by roughly three months. Half a million dollars, because nobody asked: "Have you actually tested a full restore?"
Dom's Rule of Thumb
"If it's untested, it's not working. Backed-up data that's never been restored — does it really exist? I call it Schrödinger's Data."
This applies to everything: backups, firewalls, endpoint protection, disaster recovery plans. If you're seeing a dashboard but have never validated the control, you're running on hope — not security.
The Root Cause Wasn't Technical — It Was Organizational
What struck me about this story is that it wasn't a technology failure. There was no sophisticated ransomware gang, no zero-day exploit. It was a breakdown in trust, accountability, and governance.
The IT person reported to the CFO. The CFO didn't know what to ask. The board had never discussed cybersecurity. Nobody was holding anyone accountable, and blind trust filled the gap where due diligence should have been.
Dom put it perfectly: this wasn't a single neck to choke. It was systemic — multiple layers of failure, which also means multiple layers of opportunity for growth.
Credit to that CFO — he owned it. He didn't fire the IT person. He said, "I didn't realize I needed to be doing that level of due diligence." And that's exactly where a fractional technology leader adds value. Someone who can bridge the gap between the technical team and the boardroom, ask the hard questions, and translate risk into language executives can act on.
As Dom said: "You hold me accountable, I hold them accountable, and you understand from a business and risk perspective what's being done."
The Cloud Argument — Made Real
This story also reinforced something I've believed for a long time: for 95% of Alberta businesses, cloud-managed backups are going to be better than whatever you build on-premise by yourself.
I used to build data centers. I remember a Microsoft engineer walking in and saying, "I can do it better than you, Kev." It stung at the time. But when you actually look at what cloud providers invest — firmware versioning, storage replication across regions, access tiering (hot, warm, cold), immutable backups — there's no way a single IT person with a server rack can match it. (If you're evaluating the common mistakes companies make during cloud migration, this is the root of most of them.)
Even something as simple as putting your files in SharePoint with Microsoft 365 means someone else is handling replication, geo-redundancy, and recovery for you. It's not about your skills. It's about the economics of doing it well at scale.
If you're an Alberta business still running critical files on a single on-prem file server, grab our free guide — it covers exactly these kinds of technology decisions.
Running on-prem backups you've never fully tested? You're not alone — and it's fixable. Let's figure out where the gaps are before they cost you.
Book a Free Strategy CallStory Two: The SuperBox — A Trojan Horse in Your Living Room
The second half of the episode went somewhere I didn't expect — and it's a story that reframes everything we think we know about where cyberattacks happen.
For decades, the security industry has focused on hardening corporate networks. Firewalls. VPNs. Zero trust architectures. And it worked — the front door got harder to break through. So the adversaries stopped trying. Instead, they walked around to the back of the house. Literally. The new attack surface isn't the corporate data center. It's the suburbs. The cul-de-sac. The living room where an energy executive watches the game with a $300 streaming box that's quietly exfiltrating his credentials to a server in Shenzhen.
A security researcher known as D3ada55 — degree in rhetoric and propaganda from UC Berkeley, former stints at Palo Alto Networks, Google, and Apple, now a Senior Sales Engineer at CENSUS — discovered something alarming at her father's house in the U.S. Her dad, an oil and gas executive working in the American energy sector, had purchased multiple "SuperBoxes" — one for each TV. Someone at his work had told him he "needed to get one really bad."
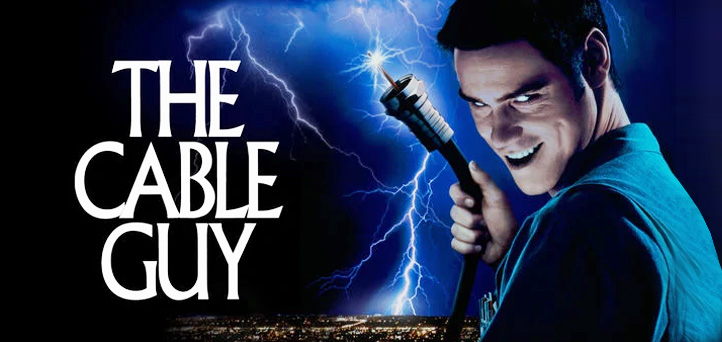
You've seen the signs. Strapped to traffic lights by the Home Depot. "Unlimited movies, $300 a year." It's the cable guy era reborn — except the guy selling you the box doesn't know he's working for a foreign intelligence operation, and the box doesn't just steal HBO. It steals everything.
D3ada55's younger sister, also studying cybersecurity, noticed the home network slowed to a crawl after the boxes arrived. That was the first clue. What she found when she started digging was a sophisticated, state-backed espionage platform masquerading as a bargain streaming device — and the attack was designed from the ground up to exploit the one place nobody secures: the home.
The Researcher Behind the Discovery
What makes this story remarkable is who uncovered it and how. D3ada55 isn't a full-time threat researcher — she does this work "for fun" alongside her sales engineering role. She's self-taught: learned packet captures using a Hak5 Packet Squirrel, taught herself to decompile Android APKs, and eventually got her GCIA certification specifically to investigate this deeper.
After presenting her findings at BSides conferences in 2023, the US Department of Defense took immediate interest. A federal investigation was opened. D3ada55 was brought in to share her network traffic logs, packet captures, and threat intelligence with authorities. For years, she was only allowed to give talks under strict rules: no cameras, no microphones, no recordings, no photos. The investigation kept her from going public until 2026.
She's also paid a personal price. After going public with her research, D3ada55 was phished and DDoSed at her own home. She now carries a Faraday bag everywhere she goes.
What the SuperBox Actually Does
Here's where it gets terrifying. When D3ada55 analyzed the device on an isolated test network, the SuperBox's behaviour was immediately hostile:
Network Reconnaissance & Attack Behaviour
- Immediate command-and-control beacon to China — The first packet out goes to Tencent infrastructure (qq.com)
- ARP flooding / denial-of-service — Sends ARP requests so aggressively it knocks other devices offline, then spoofs their MAC and IP addresses to impersonate them
- Full network enumeration — Actively nmaps and scans every device on the local subnet
- SCADA exploit attempts — Triggered a Palo Alto firewall vulnerability alert for an industrial control system exploit. Why would a TV box try this?
- Credential sniffing — Monitors the network for login traffic, banking sessions, and work credentials
Firmware & Operating System Analysis
- Deliberately outdated Android — Running a 2021 patch level, chosen specifically because it has known exploitable vulnerabilities
- Not Android TV — just Android — A suspicious choice for a "TV streaming device"
- Hidden partitions — 27 partitions in the boot structure but only 15 accessible. What's in the other 12?
- Multi-layer encoded app store — Zipped six or seven times deep as an obfuscation technique
- Root shell with no authentication — Android Debug Bridge (ADB) is open. Typing
sugives instant root access
Remote Access Infrastructure
- TeamViewer pre-installed — Allows remote desktop control of every box from a central dashboard
- Netcat available — A network utility commonly used for backdoors
- Open ports everywhere — Including on the physical remote control itself
The Remote Control Hardware
Even the remote is compromised. D3ada55 found it contains a built-in microphone (no legitimate reason for a streaming remote), a Bluetooth antenna with unusually long range (far beyond what IR or standard Bluetooth requires), self-signed certificates, and open network ports visible on internet scans. The antenna length suggests it may even be cellular-capable. It's custom hardware — it only works with SuperBox, not generic Android TV remotes.
The Perfect Trojan Horse
"It's like a perfect Trojan horse, in the traditional sense. Here's this big present… and somebody is going to hide inside."
A $300 streaming device with a botnet client, a microphone-equipped remote, and SCADA exploit capabilities sitting on the home network of an oil and gas executive. This isn't theoretical. It's happening now.
Confirmed Botnet Infrastructure
The SuperBox isn't a standalone threat. It's part of a much larger operation:
- Part of the BadBox 2.0 botnet — the continuation of the original BadBox campaign that targeted cheap Android devices
- Connected to the Aisuru-Kimwolf botnet, which was responsible for the largest DDoS attack ever recorded
- Attack capacity: 31 terabytes per second
- Botnet size: 2+ million compromised devices
- Cloudflare mitigated over 2,000 DDoS attacks from this botnet in 2025 alone
- SuperBoxes function as residential proxy nodes — attackers route traffic through home IP addresses to avoid detection
ISPs have reported massive bandwidth anomalies from SuperBox users. One customer uploaded 4,000 gigabytes in a single day. Others report hitting their allocated bandwidth cap early every billing cycle. ISPs investigating "faulty meter" complaints keep finding the same thing: a SuperBox on the network.
Why the Suburbs — Not the Server Room — Are the New Battleground
This isn't random, and it isn't just about one country's oil and gas sector. It's about a fundamental shift in how nation-state actors approach espionage. Dom and I kept circling the same realization: the suburbs have become the attack surface. The original research happened in the U.S. — but the playbook transfers directly to anywhere the energy industry operates.
Think about who lives in suburban neighbourhoods in Calgary, Edmonton, Fort McMurray, and across the WCSB. The same kinds of targets: oil and gas executives, pipeline operators, engineers with SCADA access, financial controllers who approve seven-figure invoices. Western Canada's energy sector mirrors the U.S. industry that was targeted, and these devices are sold openly online — geography is not a firewall. Every one of these high-value targets has a home network protected by nothing more than the default router their ISP handed them.
The genius of this campaign is that it bypasses corporate security entirely. Why spend months probing a company's firewall when you can put a $300 spy device on an executive's kitchen counter and let them bring the VPN tunnel to you?
- In the U.S., SuperBoxes have been mailed directly to oil and gas employees' homes — unsolicited, without anyone ordering them
- D3ada55 received reports of workers across the U.S. energy sector getting these shipped out of nowhere
- Her own father — a U.S. oil and gas executive — was told to get one by a coworker, social engineering at the workplace level
- The box immediately attempted a SCADA vulnerability exploit on the test network — targeting the exact kind of industrial control systems that run pumps, valves, and compressors
The attack vector is elegant in its simplicity. Workers bring their corporate laptops home and connect to VPNs. One report showed a SuperBox at a remote employee's house was probing their corporate network through the VPN tunnel. The box aggressively scans the network, discovers work devices, and sniffs credentials. No network segmentation at home means full visibility into work activities.
Think about that. The adversary isn't hammering the corporate firewall. They're going after the home network of a senior executive — the cul-de-sac in Tuscany, the acreage near Okotoks, the townhouse in Windermere. The places where confidential phone calls happen on speakerphone, where VPN sessions stay active for hours, and where the only "firewall" is a residential router with the default admin password still set.
Dom nailed it: this is bottom-up intelligence gathering. Don't attack the castle — attack the village where the generals live. Target workers in "positions of trust" with "privileged credentials." Someone logging into work systems from their kitchen table means credentials are exposed to anything else on that network. And if that "anything else" is a device with a microphone, a botnet client, and SCADA exploit code? Game over.
The Home-to-Corporate Attack Vector
"If you're working from home… in some type of important position where you have privileged credentials… you have this thing sitting on your network and don't know what it's potentially doing."
The original targeting happened in the U.S. energy sector — but these devices are sold across North America. For Alberta businesses with remote workers — especially in oil and gas, critical infrastructure, or any sector where people access sensitive systems from home — this is now a board-level risk. The same industries, the same roles, the same attack vector. Your corporate perimeter doesn't end at the office door. It extends to every employee's living room, every suburban router, every device on every home network. The suburbs are the new perimeter.
The MLM-Style Distribution Model
What's brilliant — and sinister — about the SuperBox campaign is how it spreads. This isn't being sold in dark web forums. It's being sold by your neighbour.
- Influencer campaigns across YouTube, TikTok, and YouTube Shorts
- MLM-style commission structure — distributors recruit resellers who recruit friends, everyone taking a cut
- Suburban family targeting — soccer moms, farmers market sellers, church groups
- Economic anxiety exploitation — "Make money on the side selling these"
- SEO poisoning — try searching for "SuperBox review." The entire first page of results is where to buy one. Zero negative content
Who's selling them? Real estate agents. Cable installers. Single moms trying to make extra cash. Retired cops. Church groups "helping people get affordable TV." Family members, gym buddies, coworkers. These aren't threat actors — they're unwitting distribution channels.
And the price itself is a tell. A comparable cheap Android streaming box costs $30–$100. A SuperBox costs $300. Where does the premium go? Into the attack infrastructure.
The Psychological Manipulation
D3ada55's background in rhetoric and propaganda (that's literally her Berkeley degree) gave her a unique lens on this campaign. She identified multiple psychological vectors:
- Implied trust: "I bought it at Best Buy, it must be safe"
- Social proof: Your neighbour sold it to you, not a shady guy in an alley
- Economic anxiety: "Save money on streaming, make money selling"
- Streaming frustration: People are sick of paying for 20 different services
- Counter-messaging: Accounts are pre-staged to shut down any negative posts the moment they appear
They even seeded fake Reddit accounts — created four years ago, never posted anything, then suddenly posted a glowing SuperBox review and went silent again. The timing aligns with the 2019–2020 campaign launch. A 2026 article in The Verge was effectively a propaganda piece making resellers look sympathetic — a retired cop helping his church get affordable TV. One seller was quoted saying, "I don't care about sending money to China." No mention of security risks anywhere in the piece.
Shell Companies and Fake Regulatory Compliance
When D3ada55 investigated the manufacturer, the trail went nowhere fast:
- The listed manufacturer is a complete shell company — stock photos on the website, template design, zero legitimate business presence
- Fake LinkedIn profiles for supposed employees
- No real corporate registration found
- The box displays FCC certification logos — but no actual FCC registration exists
- All regulatory information on the device is completely fabricated
- Import documents were signed with a qq.com email address as the "US agent"
- Fake "certificates of award" printed on the packaging to appear legitimate
Displaying fake FCC certification marks is illegal. But enforcement is essentially absent, and the shell company structure means there's no one to hold accountable.
Also Known As…
SuperBox isn't the only brand name. The same hardware and botnet infrastructure ships under multiple brands, including vSeeBox and MagaBox. If someone in your family has any of these devices, the advice is the same: unplug it immediately. Don't just move it to a guest network — remove it from your home entirely.
What IT Security Teams Should Look For
If you're on a security team — especially at an energy company, critical infrastructure operator, or any organization with remote workers — here are the detection indicators Dom and I discussed:
Network Detection Indicators
- Excessive ARP requests from a single device — these boxes ARP flood aggressively and cause other devices to lose DHCP reservations
- Connections to qq.com, Tencent IPs, and .top domains — common SuperBox command-and-control destinations
- Android Debug Bridge traffic (port 5555) from consumer devices — should not exist on any network
- TeamViewer connections from non-workstations — major red flag
- SCADA-related vulnerability signatures originating from consumer devices — this alone should trigger an incident
- Unusual upstream bandwidth consumption — look for residential users exceeding normal upload patterns
- MAC address OUI lookup — manufacturer will show a suspicious Chinese ODM, not a recognizable consumer brand
For Leadership and Executives
- Oil and gas is being specifically targeted. This is not random. These devices are being mailed to employees' homes.
- Someone on your team may have recommended these. D3ada55's father got his recommendation from a coworker.
- VPN doesn't protect you here. The box is inside the VPN tunnel, probing corporate resources from within the trusted network.
- SCADA implications are real. The box attempted SCADA exploits immediately on first boot. If your organization operates industrial control systems, this is a critical risk.
For Individuals and Families
- Ask your family. Check if anyone has a "SuperBox," "vSeeBox," or "MagaBox." Especially older relatives.
- If you see one, unplug it. Don't put it on a guest network. Remove it from the home entirely.
- Segment your network. IoT devices should never be on the same network as work laptops. Ever.
- Price isn't an indicator of safety. The $300 box is actually more dangerous than the $30 one — the premium funds the attack infrastructure.
Words That Should Set Off Alarm Bells
Dom made a point that deserves its own callout: if you're a technical person, stop saying "state of the art." And definitely stop saying "it should work."
To trained ears — whether it's your fractional CTO, your auditor, or your CISO — those words signal uncertainty, not confidence. Either you understand how a system works or you don't. There's no middle ground when you're responsible for protecting an organization's data and operations.
It's better to say "I don't know" and go find the answer than to project false confidence that collapses under scrutiny.
Key Takeaways for Business Leaders
- Test your backups. Regularly. A backup that hasn't been restored is a hope, not a plan. Run full tabletop exercises. Bring in a third party to validate.
- Don't confuse a dashboard with security. Deploying EDR or a firewall doesn't mean it's working. Continuous validation testing is where the industry is headed — and where AI can play a massive role.
- Boards need to talk about cyber. If your board minutes don't mention cybersecurity, you have a governance gap. Executives are accountable for due diligence, not just the IT team.
- Audit every device on your network — including at home. If your team works remotely, home network hygiene is now a corporate security concern. Know what's connected.
- The home is the new perimeter. Remote work means your attack surface extends to every employee's living room. Network segmentation, device audits, and employee awareness aren't optional anymore.
- Get an independent advisor. Whether it's a fractional CTO or a fractional CISO, having someone who can bridge the technical-to-boardroom gap is the difference between a $500K lesson and a proactive strategy.
Timeline: The SuperBox Investigation
- 2019 SuperBox campaign launches — fake Reddit accounts seeded for social proof
- 2021 Android patch level deliberately chosen for devices (known vulnerabilities)
- 2021 D3ada55 discovers the boxes at her father's house
- 2023 Deep technical research begins — GCIA certification obtained for investigation
- 2023 First BSides talk — federal investigation opened by US government
- 2025 D3ada55 joins CENSUS, discovers vSeeBox and MagaBox variants
- Jun 25 FBI issues PSA: "Home Internet Connected Devices Facilitate Criminal Activity"
- Fall 25 Krebs on Security publishes investigation — residential proxy network link confirmed
- Late 25 D3ada55 is phished and DDoSed at home after going public
- Jan 26 Kimwolf botnet launches largest DDoS attack ever recorded — 31 TB/sec
- 2026 The Verge publishes pro-SuperBox propaganda article with zero security context
Further Reading & Resources
- Krebs on Security — Android TV Streaming Box Botnet
- FBI IC3 PSA — IoT Devices Facilitate Criminal Activity (June 2025)
- Matt Brown (YouTube) — SuperBox Technical Analysis
- CENSUS (censys.io) — Internet intelligence platform used in the investigation
- Spur.us — Residential proxy network hunting platform
Frequently Asked Questions
What is a SuperBox and why is it dangerous?
A SuperBox is a jailbroken Android streaming device sold for around $300 that promises unlimited free TV. Security research has revealed these devices contain pre-installed malware — TeamViewer for remote access, credential-sniffing tools, and SCADA exploit code. They beacon to command-and-control servers in China, perform aggressive network scans, and function as nodes in the BadBox 2.0 and Aisuru-Kimwolf botnets. The FBI issued a public service announcement about these devices in June 2025.
Why are SuperBoxes targeting oil and gas workers?
SuperBoxes have been mailed directly to oil and gas employees' homes — sometimes unsolicited. The devices attempt SCADA vulnerability exploits on first boot, targeting the industrial control systems used in energy infrastructure. When workers connect to corporate VPNs from home, the SuperBox probes the corporate network through the VPN tunnel. This is bottom-up intelligence gathering: target workers with privileged access at home, where security is weakest.
How do I know if a SuperBox is on my network?
Look for excessive ARP requests from a single device, connections to qq.com or Tencent IP addresses, Android Debug Bridge traffic on port 5555, TeamViewer connections from non-workstations, and unusual upstream bandwidth. A MAC address OUI lookup showing a suspicious Chinese ODM is a strong indicator. Also check for devices branded as vSeeBox or MagaBox — same hardware, same botnet.
How often should businesses test their backups?
Full restore tests at least quarterly. Tabletop disaster recovery exercises at least annually. Any architecture change triggers an immediate validation test. A backup that has never been restored is Schrödinger's Data — it might work, it might not, and you won't know until it's too late. One company learned this the hard way with a $500,000 penalty.
Is putting a SuperBox on a guest network enough?
No. The device contains a microphone-equipped remote, a long-range Bluetooth antenna, and potentially cellular capability. Guest network isolation doesn't address audio surveillance or out-of-band communication. Unplug it entirely and remove it from your home.
What's Next
Firewall Fridays continues — Dom and I are recording these monthly, and it's quickly becoming one of the most popular segments on the Code to Cloud podcast. If you're a business owner, tech leader, or IT professional in Alberta or Western Canada, join our Discord community where these conversations keep going between episodes.
And if this episode hit home — if you're not sure whether your backups actually work, or you're wondering what's lurking on your network — that's exactly the kind of thing we help businesses figure out. Book a free strategy call and let's talk.
Know someone in oil and gas who needs to hear this? Send them this article. The SuperBox story is the kind of thing that protects people when it gets shared — not when it stays in a browser tab.
